Post-Quantum Systems
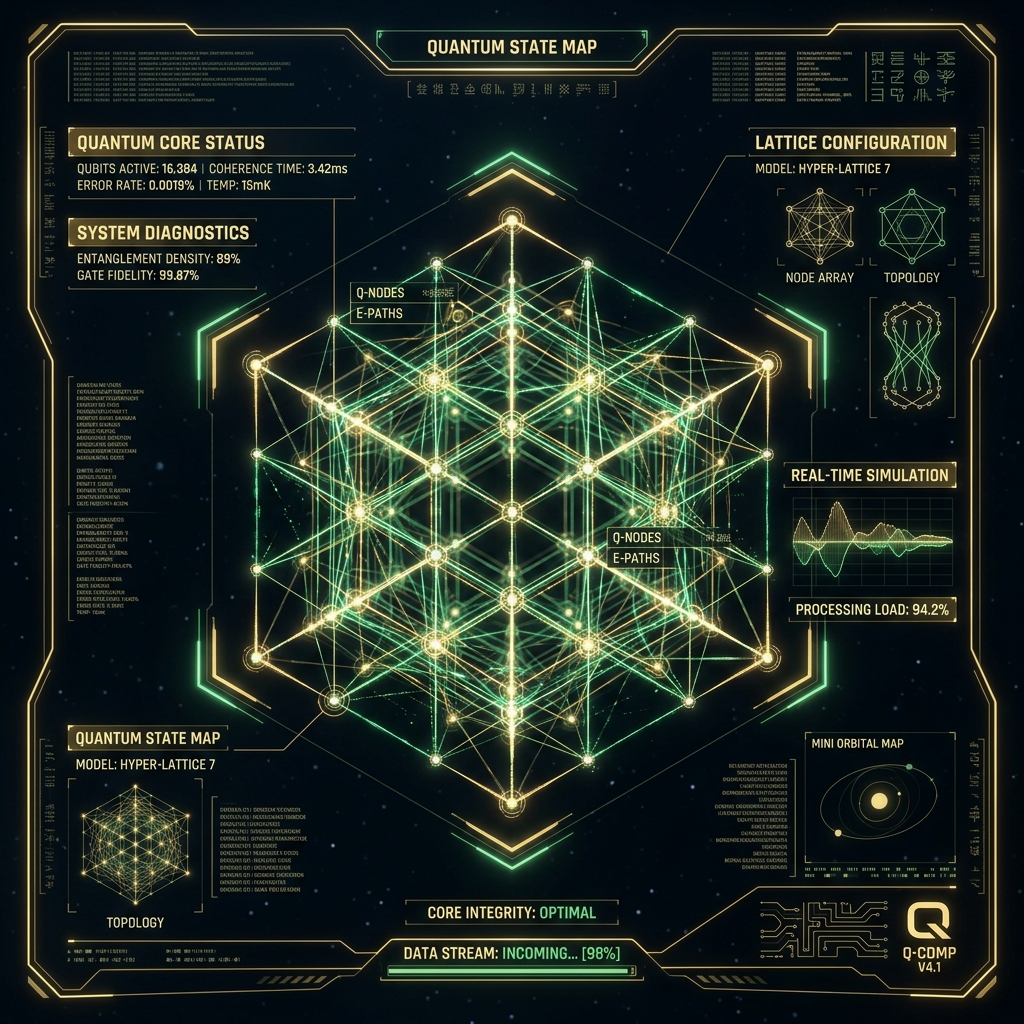
Current cryptographic standards will break under quantum computation. We architect blockchain systems fortified with lattice-based cryptography, hash-based signatures, and quantum-resistant key exchange protocols — designed to survive the transition, not react to it.
Access Protocol



